2022 - II Quarterly Bulletin
C3 TOP – Threat Observatory Platform
Threat Agent activities
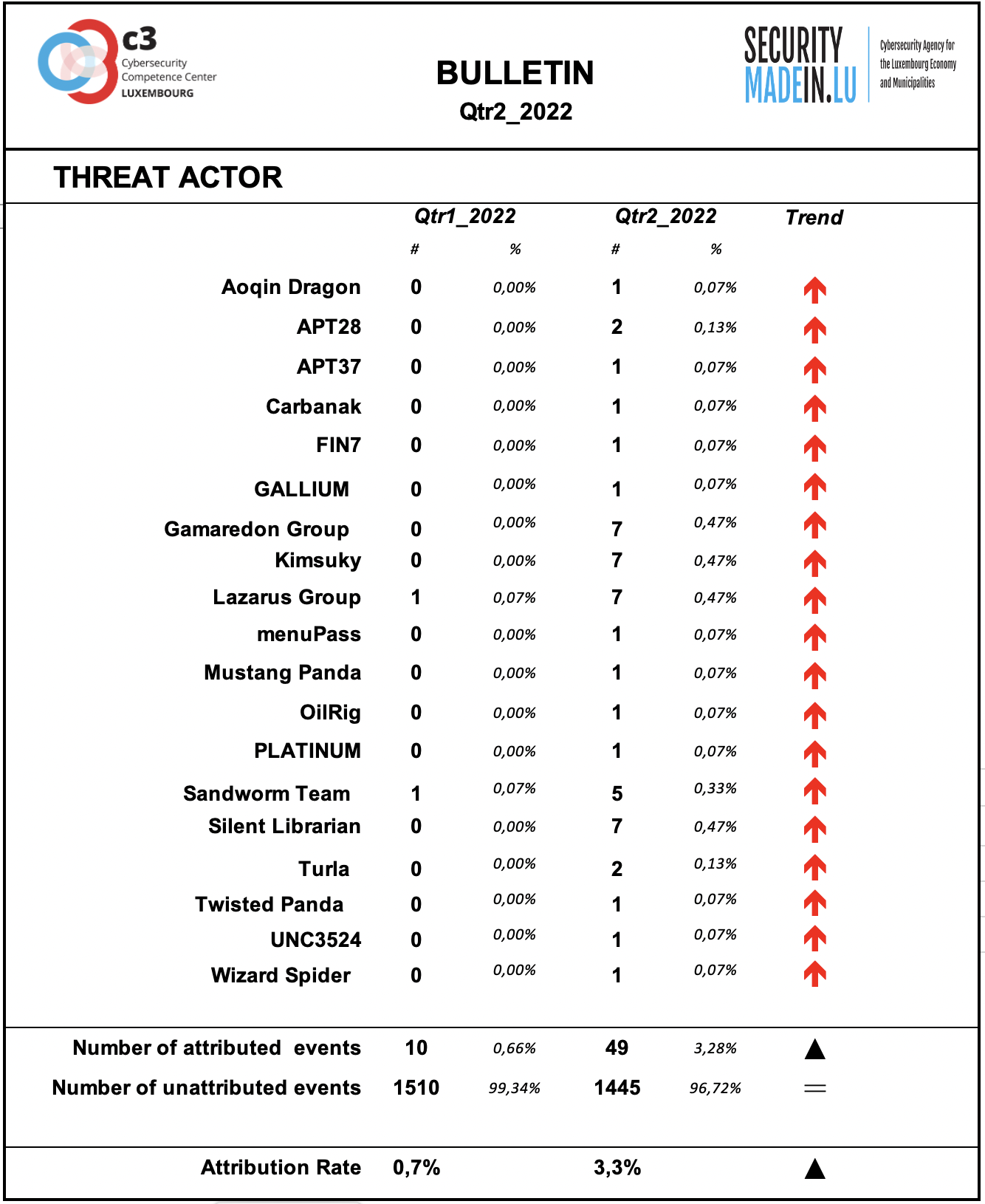
Behind every cyber-attack there is an actor with a specific intent. However, for many events, the identity and general motivation are unknown. On the other hand, some groups have been well known for years and their criminal activities and techniques are documented and monitored. Typically, they conduct targeted attacks against specific organisations, using relatively sophisticated tools and attack procedures.
Some of them are considered as State-sponsored, but the actual link with various countries stays often subject of controversies and should be considered with prudence.
During the second quarter of 2022 has been observed a significant increase of identifiable threat groups’ activity.
As during previous quarters, the attribution rate of events is very low. This means that most of the ongoing attacks are not attributable.
According to the attribution found in the MISP records, the following groups were particularly active during this quarter:
APT28 is a threat group that has been attributed to Russia's General Staff Main Intelligence Directorate (GRU) 85th Main Special Service Center (GTsSS) military unit 26165. This group has been active since at least 2004. Some of its activities are conducted with the assistance of GRU Unit 74455, which is also referred to as Sandworm Team.
FIN7 is a financially-motivated threat group that has been active since 2013 primarily targeting the U.S. retail, restaurant, and hospitality sectors, often using point-of-sale malware.
Gamaredon Group has been active since at least 2013 and has targeted individuals likely involved in the Ukrainian government;
Group5 is a threat group with a suspected Iranian nexus, though this attribution is not definite. The group has targeted individuals connected to the Syrian opposition via spearphishing and watering holes, normally using Syrian and Iranian themes.
Kimsuky North Korea-based cyber espionage group that has been active since at least 2012. The group initially focused on targeting South Korean government entities, think tanks, and individuals identified as experts in various fields, and expanded its operations to include the United States, Russia, Europe, and the UN. Kimsuky has focused its intelligence collection activities on foreign policy and national security issues related to the Korean peninsula, nuclear policy, and sanctions;
Lazarus group is a North Korean state-sponsored cyber threat group; it uses a wide range of methods depending on the characteristics of the campaigns carried out and the objectives pursued. It mainly aimed at manipulating employees of strategically important companies such as those involved in the military or aerospace industry;
Sandworm Team is a destructive threat group that has been attributed to Russia's General Staff Main Intelligence Directorate (GRU) Main Center for Special Technologies (GTsST) military unit 74455. This group has been active since at least 2009. In October 2020, the US indicted six GRU Unit 74455 officers associated with Sandworm Team for the following cyber operations: the 2015 and 2016 attacks against Ukrainian electrical companies and government organizations, the 2017 worldwide NotPetya attack, targeting of the 2017 French presidential campaign, the 2018 Olympic Destroyer attack against the Winter Olympic Games, the 2018 operation against the Organisation for the Prohibition of Chemical Weapons, and attacks against the country of Georgia in 2018 and 2019. Some of these were conducted with the assistance of GRU Unit 26165, which is also referred to as APT28.
Silent Librarian is a group that has targeted research and proprietary data at universities, government agencies, and private sector companies worldwide since at least 2013. Members of Silent Librarian are known to have been affiliated with the Iran-based Mabna Institute which has conducted cyber intrusions at the behest of the government of Iran, specifically the Islamic Revolutionary Guard Corps (IRGC).
Turla is a Russian-based threat group that has infected victims in over 45 countries, spanning a range of industries including government, embassies, military, education, research and pharmaceutical companies since 2004 is a cyber espionage group operating against targets in East Asia, particularly Taiwan, and occasionally, Japan and Hong Kong. Based on the mutexes and domain names, BlackTech’s campaigns are likely designed to steal their target’s technology;
It should be noted that has been also recorded an event attributed to UNC3524. Mandiant observed this group operating since December 2019. Its techniques partially overlap with multiple Russian-based espionage actors (APT28 and APT29). They are described as having a high level of operational security, low malware footprint, adept evasive skills, and a large Internet of Things (IoT) device botnet at their disposal. This confirms the activities of Russian groups during this period.
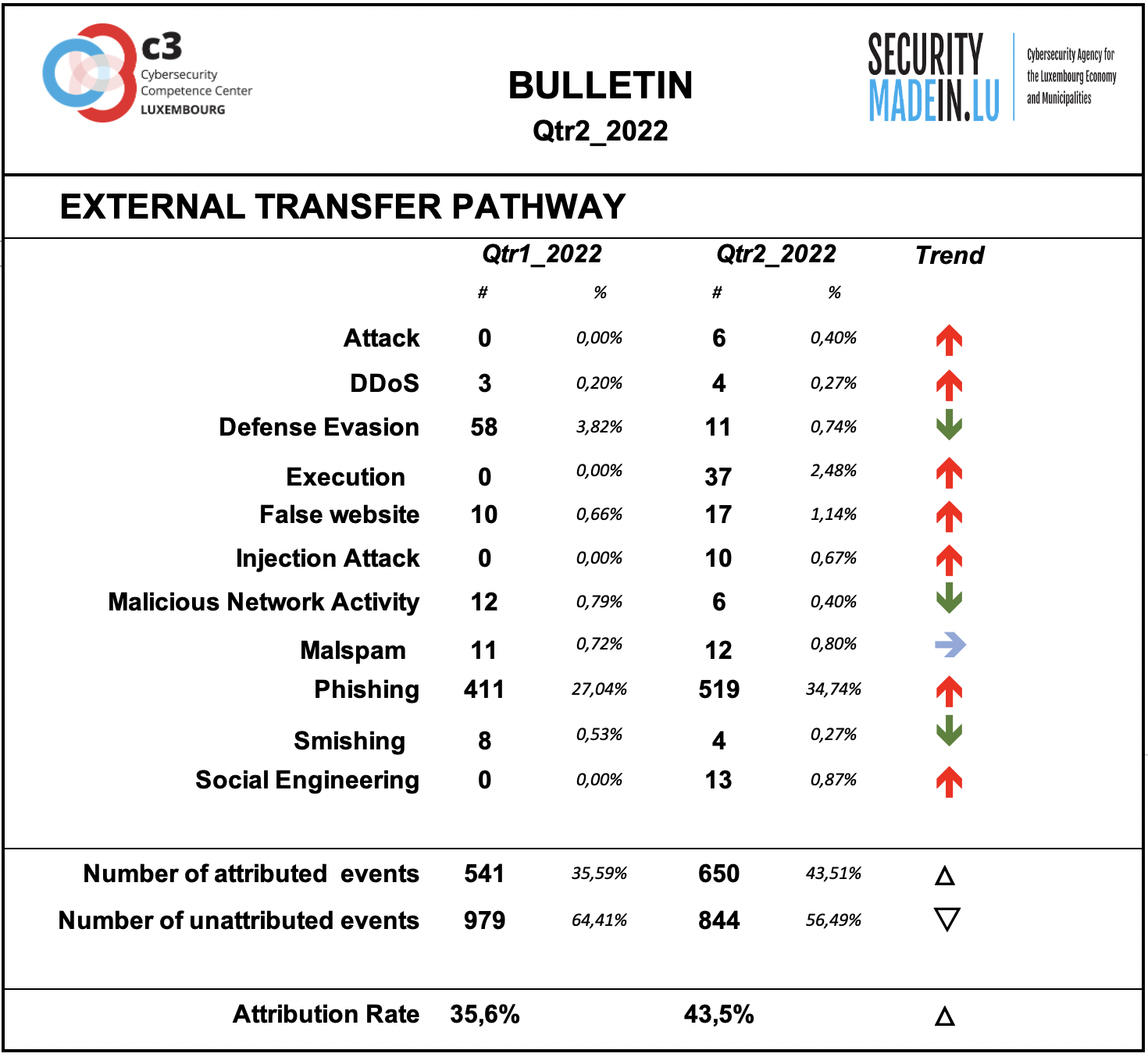
External transfer pathway and infrastructures
The transfer of the malicious artefacts or payloads is done through a number of different types of technical procedures and infrastructures.
Also, during the second quarter of 2022, it is confirmed that the most frequently used strategy is associated with scams that use email or similar approaches to reach potential victims.
Phishing is the most common strategy, but other scam strategies are also recorded.
It should be noted that during this period two attacks concerned the exploitation of the vulnerability of network port 443 to conduct an SSRF (Server Side Request Forgery) attack on an Exchange server. The attacker targets an application that supports data imports from URLs or allows them to read data from URLs. URLs can be manipulated, either by replacing them with new ones or by tampering with URL path traversal.
The attribution rates are significantly better than for threat actors, even if still fairly low. Attribution means that it was possible to identify the external transfer pathway for a given event.
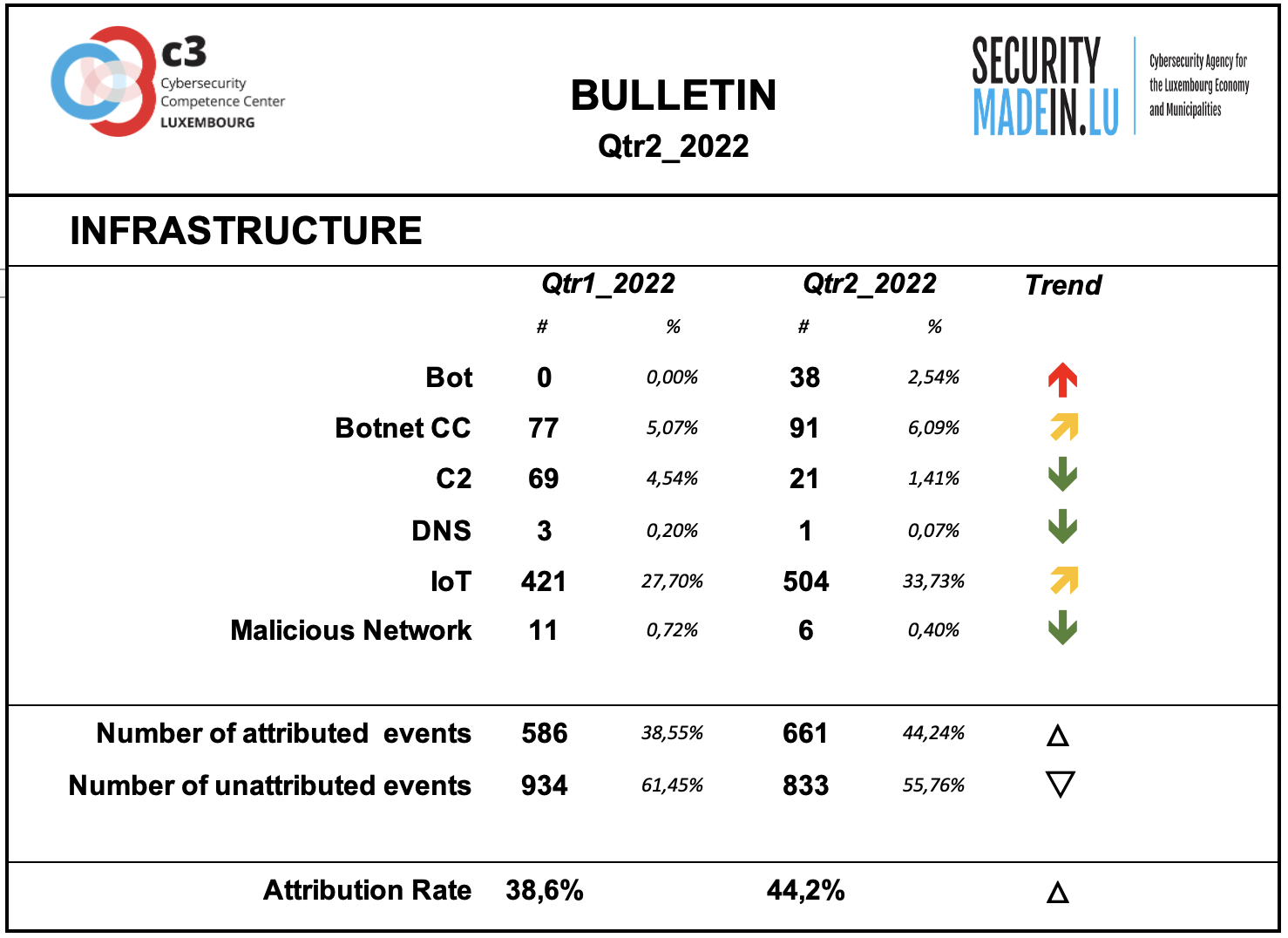
Infrastructures represent the type of systems being used for supporting attacks. Some are meant to compromise or help compromise, the targeted system, others are more focused on helping to maintain the foothold in it. Indeed, once access to a system device has been gained, a communication channel is maintained through the use of command and control (C2) infrastructures. The specific mechanisms vary greatly between attacks, but C2 generally consists of one or more covert communication channels between devices in a victim organization and a platform that the attacker controls. These communication channels are supporting the malicious activities. They are used to issue instructions to the compromised devices, download additional malicious payloads, and pipe stolen data back to the cyber-actor.
During this period there was a significant increase in events using bot, i.e. autonomous programs that can interact with systems or users and that can support malicious activities.
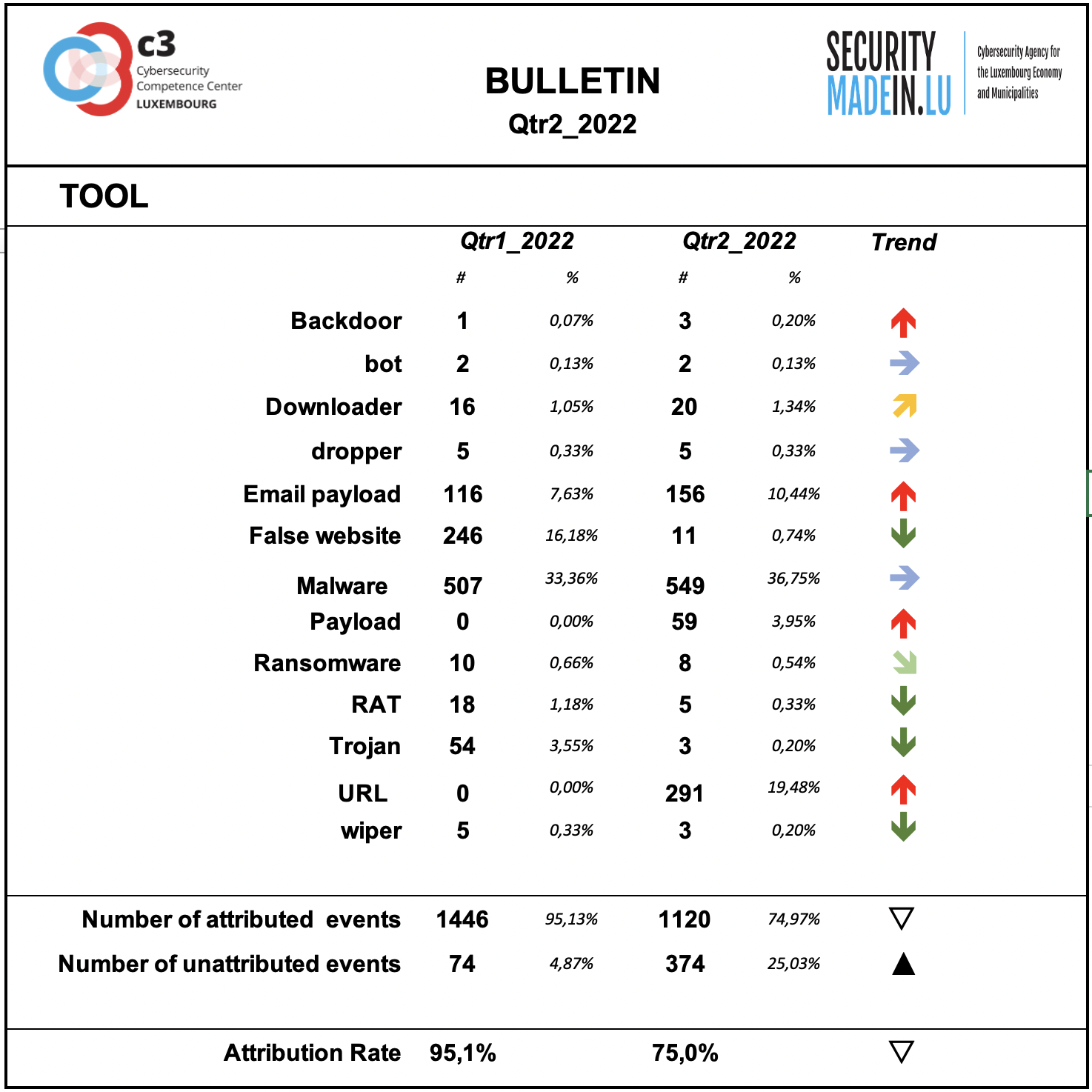
Tool
The monitoring system showed a substantial prevalence of the use of Malware especially associated with IoT systems.
The monitoring systems have recorded an increase in the use of malicious URL and False Websites.
Points of access
The most common access point reported by MISPPRIV users is e-mail, which isn’t too surprising as it’s an effective ingress vector for several types of attacks. It’s often exploiting users’ weaknesses, be they voluntary (negligence) or involuntary (lack of knowledge about a specific threat.
During this period the attribution rate has increased significatively.
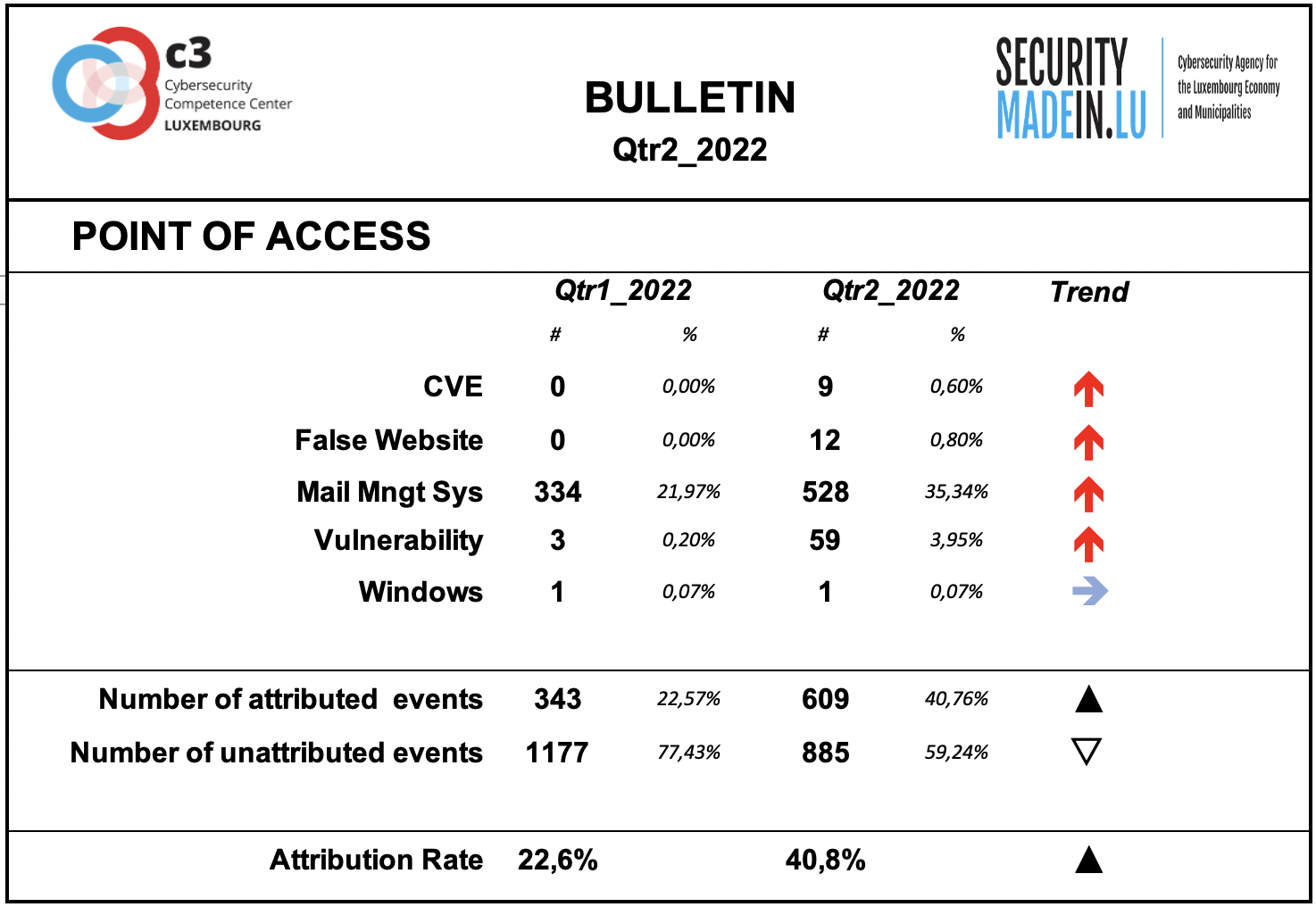
With regard to component and system vulnerabilities, the monitoring system identified the following:
Object-Graph Navigation Language for open-source Expression Language (EL) of Java objects;
Number of vulnerabilities associated to Microsoft Exchange;
Apache Log4j Remote Code Execution Vulnerability.
a new zero-day remote code execution (RCE): it is called Follina and the successful exploits of this vulnerability can allow running arbitrary code with the privileges of the calling application. The attacker can then install programs, view, change, or delete data, or create new accounts in the context allowed by the user’s rights.
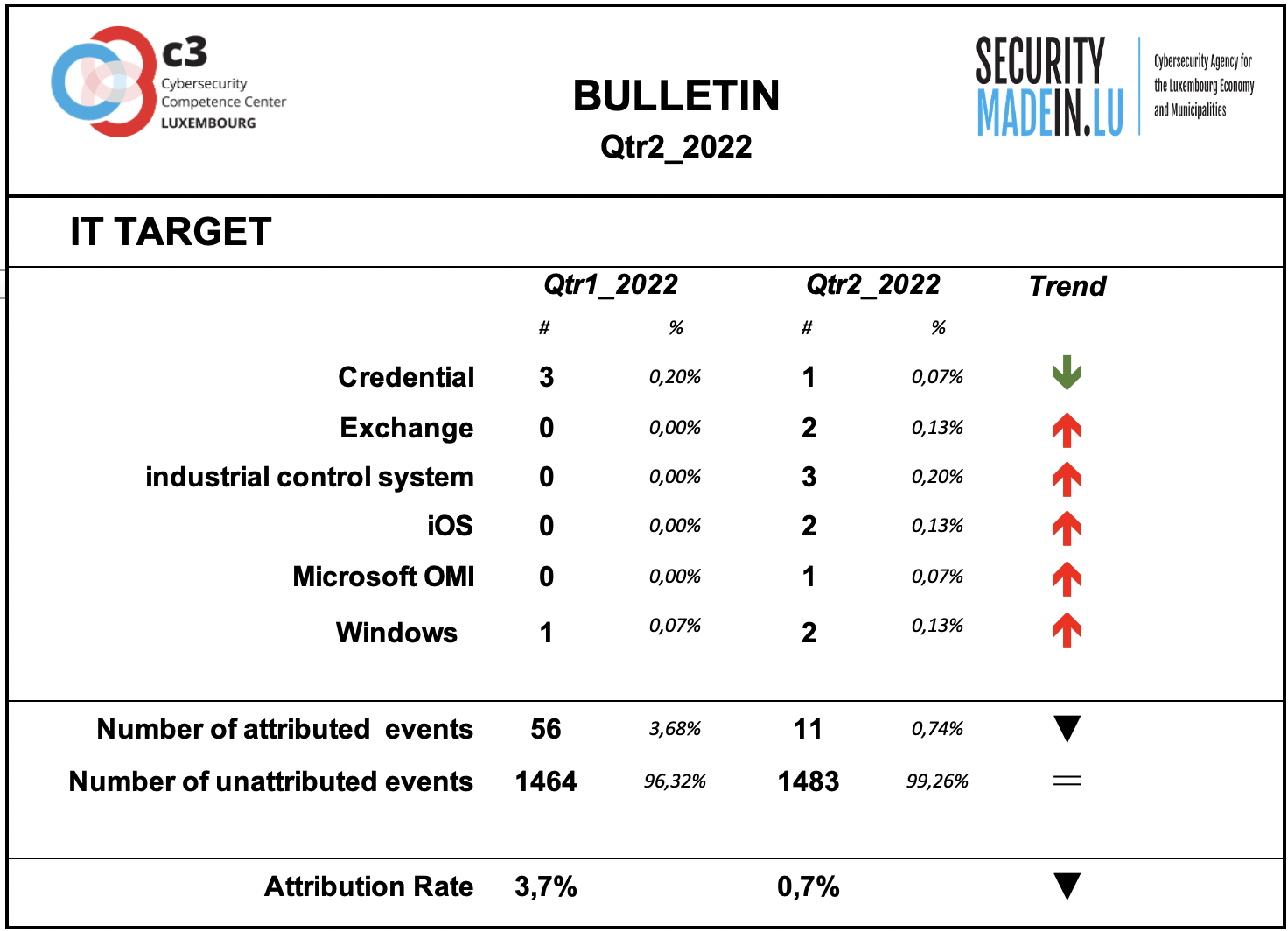
IT Target
Information on the attacked IT target is not sufficiently described by the analysed events.
It should be noted that there is still some residual evidence of the attack campaign related to the exploitation of a number of vulnerabilities in the Microsoft Exchange Server system.
During this period some attacks on ICS (Industrial Control System) have been recorded.
An event involving Microsoft's OMI system was also detected. Multiple critical vulnerabilities of Microsoft Open Management Infrastructure (OMI) allow an attacker to escalate privileges and execute arbitrary code on the affected system.
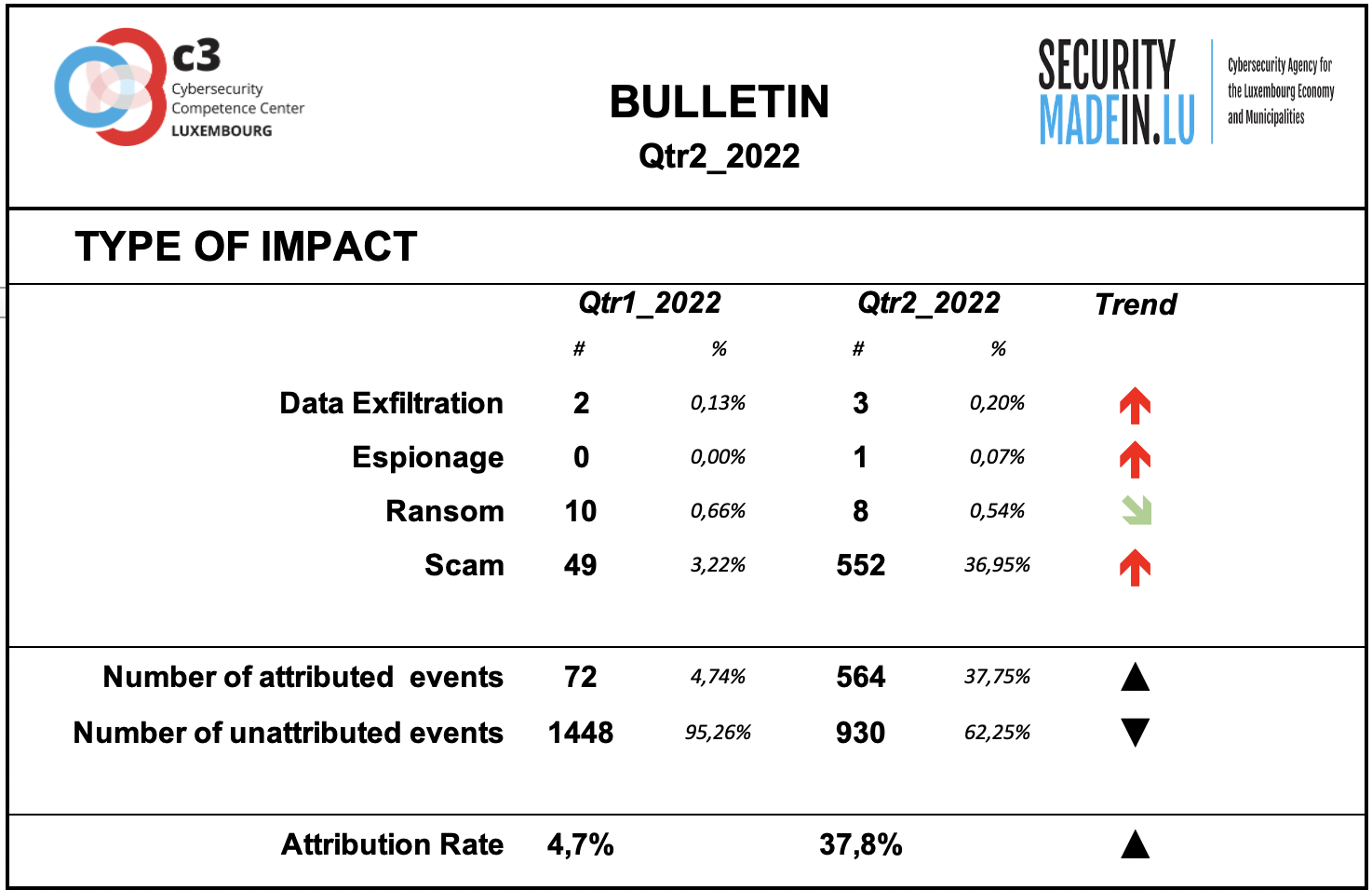
Type of Impact
The information detected by the monitoring system regarding the type of consequences for the victim is mainly related to ransom demands.
The high number of scams is strictly related to the classification of phishing records as scam events. Therefore, the attribution rate of this class remains rather low.
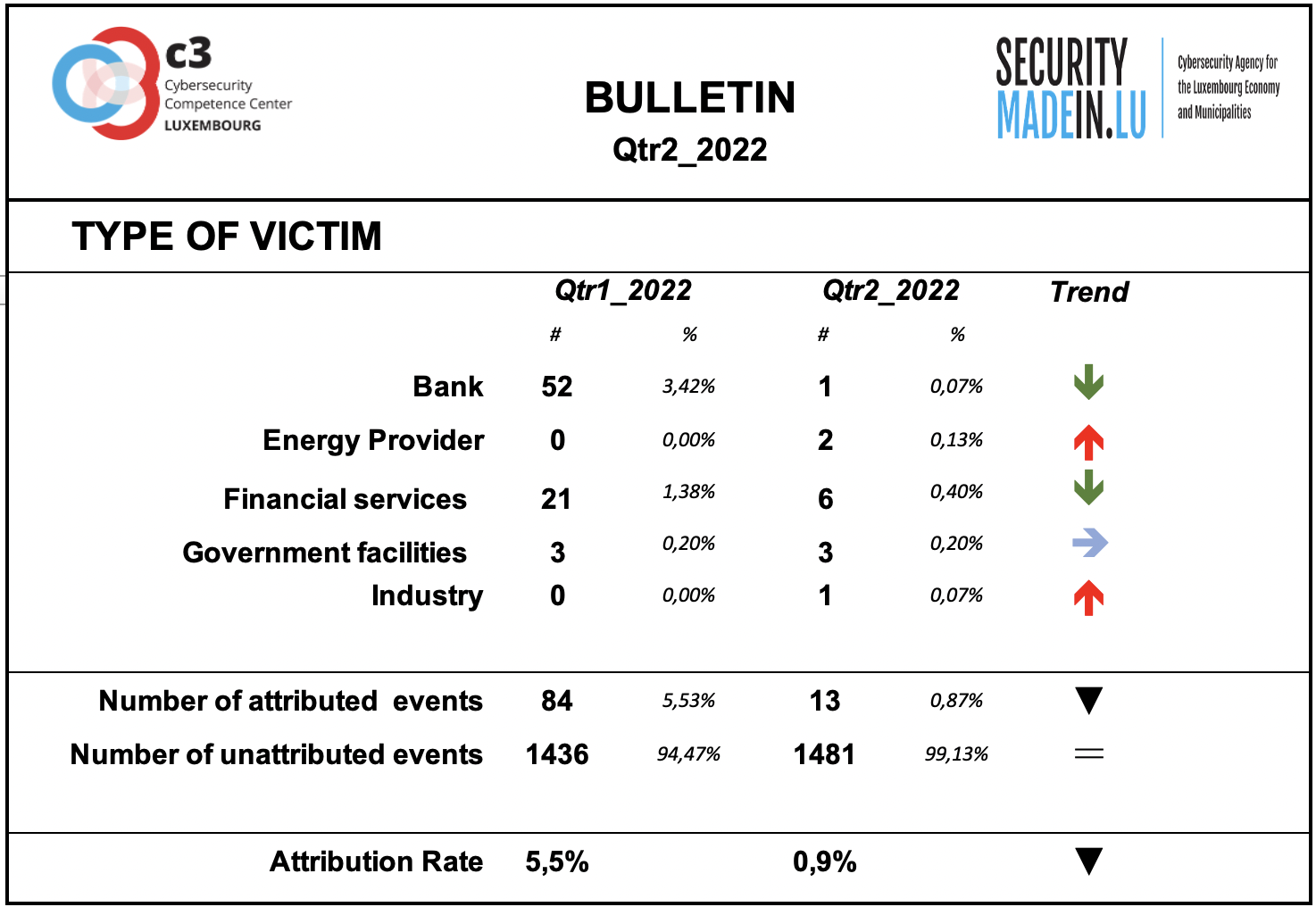
Type of Victim
During this quarter there was a significant reduction in the number of events detailing the type of victim affected.